Software patches 101 is your essential starting point for understanding how patches, updates, and the broader discipline of software maintenance work together to keep complex IT environments secure, compliant, and resilient in the face of evolving threats and unpredictable user workloads. By clarifying the difference between routine updates and targeted fixes, it helps teams prioritize risk, align with governance requirements, and tighten patch management practices across heterogeneous systems, from on-prem data centers to cloud-based services. The core benefits include reduced exposure to exploits, fewer disruptions, faster remediation cycles, and steadier performance through timely software updates that minimize user-facing risks while supporting ongoing business operations. This guide outlines practical steps for testing, approving, and deploying patches with minimal user impact, emphasizing change control, rollback planning, and clear communication with stakeholders about expected behavior. Ultimately, a disciplined patching routine strengthens resilience, reduces risk, and helps protect data without compromising productivity, enabling IT teams to respond quickly to new vulnerabilities and evolving software landscapes.
In other terms, this topic translates into vulnerability remediation, prioritization by risk, and a proactive stance toward patching rather than reactive firefighting. A broader view reframes the patching lifecycle as part of a security patches program, emphasizing governance, testing, and staged rollout to reduce surprises. Viewed through this lens, teams rely on the operational engine that inventories assets, schedules deployments, and verifies effectiveness. By integrating these ideas, organizations can demonstrate compliance readiness, maintain uptime, and respond swiftly to evolving threats. This framing supports clear, actionable steps for teams and helps leadership see patching as an ongoing risk-reduction program.
Software patches 101: Core concepts for security, updates, and resilience
Software patches 101 introduces the idea that patches, updates, security patches, and bug fixes are essential for reducing risk and maintaining reliability. In practice, this means aligning patch management with security goals and the software lifecycle to minimize exposure to threats and glitches.
By treating patches as part of a broader vulnerability remediation strategy, teams can address known weaknesses in a controlled way, prioritizing security patches and software updates that close CVEs and prevent exploit chains. This holistic view strengthens resilience and supports ongoing compliance with governance requirements.
A practical patch management framework for modern IT environments
Patch management is a repeatable process comprising discovery, inventory, vulnerability assessment, testing, deployment, and monitoring. This framework ensures that security patches and bug fixes are applied consistently across on-premises and cloud assets, reducing the attack surface without sacrificing availability.
Effective patch management also fosters governance and compliance, with documented timelines and evidence of remediation, asset hygiene, and ongoing vulnerability remediation. Organizations that standardize these steps tend to improve risk posture and demonstrate due diligence to auditors and stakeholders.
Security patches vs. updates vs. bug fixes: defining roles and priorities
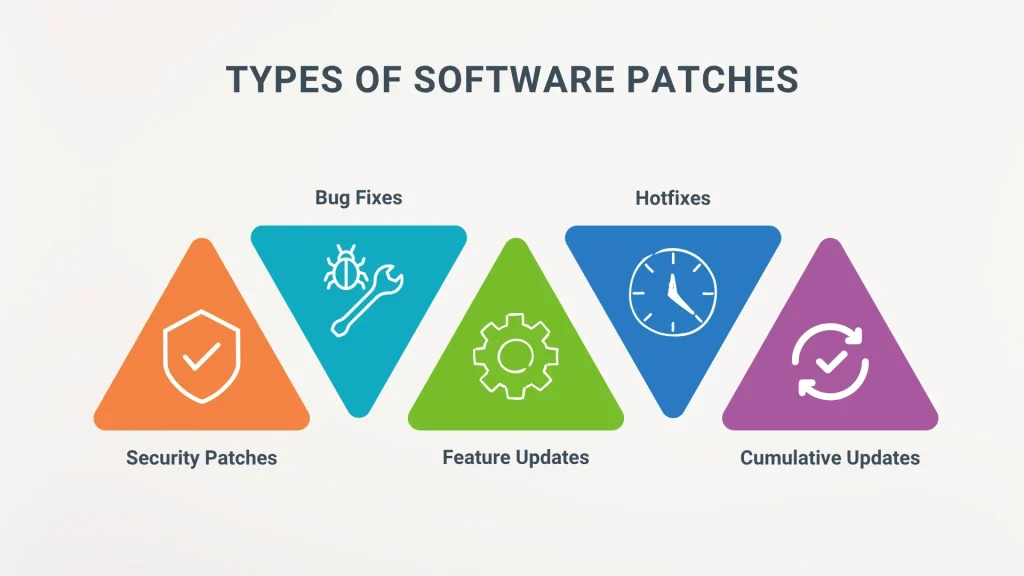
Updates often focus on features and performance, while security patches fix exploitable weaknesses that threat actors target. Bug fixes improve reliability and data integrity, and together they form a coordinated patching plan that balances risk and value.
Understanding these distinctions helps prioritize risk: security patches and vulnerability remediation take precedence, while feature updates are scheduled to minimize downtime. Clear categorization supports faster decision-making and more predictable maintenance windows.
Deployment strategies that minimize risk and disruption
Automatic updates, staged rollouts, maintenance windows, and defined rollback plans enable rapid remediation without disrupting users. Choosing the right strategy depends on system criticality, change impact, and the organization’s tolerance for downtime.
A disciplined approach to patch deployment supports patch management goals, reduces the window of exposure to known vulnerabilities, and aligns with governance policies. Regular testing and rollback testing ensure quick recovery if a patch introduces unforeseen issues.
Measuring success with metrics, dashboards, and governance
Key metrics include patch cadence, time-to-patch for security patches, and coverage across critical systems, contributing to stronger vulnerability remediation outcomes. Dashboards that track vulnerability scanning results and remediation progress help security teams stay accountable.
Auditable artifacts, vulnerability scanning results, and compliance reporting demonstrate how software updates and bug fixes translate into tangible risk reduction. Regular reviews of these metrics support continuous improvement and demonstrate governance to leadership.
Tools, automation, and best practices for efficient patch management
Asset inventory tools, vulnerability scanners, patch management solutions, and change management processes automate discovery, testing, deployment, and rollback. Integrating these tools creates a cohesive workflow that reduces manual errors and accelerates remediation.
Adopting automation improves reliability, speeds vulnerability remediation, and helps maintain a sustainable cadence for software updates, security patches, and bug fixes. Best practices include risk-based prioritization, quarterly patch cadences, and a robust rollback strategy to protect operations.
Frequently Asked Questions
What is Software patches 101 and why is patch management essential for security patches and vulnerability remediation?
Software patches 101 provides the basics of patches, including updates, security patches, and bug fixes. Patch management is the ongoing process of discovering, testing, deploying, and monitoring patches across an IT environment to reduce risk and protect data. Focusing on security patches and vulnerability remediation helps minimize exploit windows and downtime.
In Software patches 101, how do software updates, security patches, and bug fixes differ and why does this distinction matter for risk management?
Software updates add features, improvements, and sometimes minor security tweaks. Security patches specifically fix vulnerabilities that threat actors could exploit, often driven by CVEs. Bug fixes address defects to improve stability and data integrity. Understanding these differences in Software patches 101 helps teams prioritize risk, allocate resources, and communicate with stakeholders.
What is the practical patch management framework described in Software patches 101?
A practical framework includes inventory and discovery, vulnerability assessment, patch selection and testing, deployment and change management, verification and monitoring, and documentation and governance. Automation and standardized processes help patch faster while reducing the risk of outages.
What patch deployment strategies does Software patches 101 recommend and when should you use them?
Strategies include automatic updates for less-critical systems, staged rollout to limit risk, maintenance windows to minimize user impact, and clear rollback procedures for critical patches. Software patches 101 also highlights prioritizing high-severity patches and using automation to coordinate testing, deployment, and rollback.
Why do security patches demand prompt attention in Software patches 101, and how does vulnerability remediation fit into the process?
Security patches are the frontline defense against attackers; a single unpatched vulnerability can cause breaches and downtime. In Software patches 101, vulnerability remediation is driven by risk-based prioritization, rapid testing, and clear communication with stakeholders about reboots or maintenance, ensuring timely deployment.
What best practices from Software patches 101 help maintain effective patch management and avoid common pitfalls?
Best practices include maintaining an up-to-date asset inventory, using vulnerability scanners, centralized patch management solutions, and strong change-management and governance. Build testing environments, monitor after deployment, and have rollback plans. Common pitfalls to avoid are compatibility issues, downtime, patch fatigue, incomplete rollback plans, and poor visibility into endpoints.
| Aspect | Key Points |
|---|---|
| What patches cover | Patches include updates, security patches, and bug fixes; these play distinct roles and together reduce risk, minimize downtime, and support compliance. |
| Updates | Add features, improve UX/performance; may include minor security improvements; primary aim is value, not risk mitigation. |
| Security patches | Fix vulnerabilities; often prioritized due to risk; may reference CVEs and known weaknesses; reduces exploit window. |
| Bug fixes | Address defects causing crashes, incorrect behavior, or data integrity issues; improves stability and trust. |
| Overlap | A patch can include updates, security improvements, and bug fixes; treating categories distinctly aids prioritization and communication. |
| Patch management framework | Discovery, testing, deployment, and monitoring across IT environments; steps include inventory, vulnerability assessment, testing, deployment, verification, and governance. |
| Deployment strategies | Automatic updates; staged rollout; maintenance windows; critical patch prioritization; rollback and testing. |
| Security patch urgency | Frontline defense against attackers; unpatched vulnerabilities lead to breaches; use vulnerability scanning and rapid testing; clear communication with users about reboots or downtime. |
| Updates & bug fixes for reliability | Updates can indirectly improve security; bug fixes boost reliability and user satisfaction; patch cycles should treat both as a package. |
| Tools & best practices | Asset inventories, vulnerability scanners, patch management solutions, change management, testing environments, monitoring/telemetry, governance; establish cadence and a kill switch for rollback. |
| Common pitfalls | Compatibility issues, downtime, patch fatigue, inadequate rollback plans, limited visibility into endpoints; mitigations include testing, staged rollouts, backups, and reporting. |
| Practical routine & governance | Daily risk checks, weekly asset hygiene, monthly patch cycles, quarterly security review; align with governance and incident response playbooks. |
Summary
Software patches 101 lays the foundation for building resilient software environments. By distinguishing updates from security patches and bug fixes, organizations can prioritize risk, streamline deployment, and maintain high reliability. A robust patch management program—encompassing asset inventories, vulnerability assessments, testing, and governance—reduces exposure to exploits and operational disruptions. Patches, when applied thoughtfully, strengthen security, improve performance, and protect stakeholders’ trust. Embracing a proactive Software patches 101 mindset helps teams navigate evolving threats and ensure smoother IT operations, regulatory compliance, and user satisfaction.